
When using Azure DevOps you will likely need to use secrets within your Pipeline.
There are a number of ways in order to this. For example, you can define Secure Pipeline variables:

However, particularly where you may be using the same secrets in a number of areas across your eco-system – e.g. References in ARM templates, secret values used in App Settings, as well is when used in your Pipeline – it is preferable for a single source of truth.
Another alternative is to call from the keyvault within your Pipeline at runtime, as a Release task, and making use of this as a variable updated or defined on-the-fly:
We can call the secrets from the KeyVault

…and then use the obtained secret

Both of these methods are perfectly legitimate means of consuming secrets within your Pipeline. However, when using secrets that are already stored in Keyvault, I prefer to reference these directly using Variable Groups.
Firstly, here is an example of secrets in KeyVault:

In order to commence the link to the secrets, create a new Variable Group within the Library tab on Azure DevOps:

Then it’s a matter of making reference to the KeyVault:

Make sure that your Azure DevOps Service Connection has permissions to Get and List the secrets from the KeyVault. An Access Policy on the KeyVault will resolve this:

Alternatively, you can script the Access Policy, via Powershell:
$ErrorActionPreference="Stop";Login-AzureRmAccount -SubscriptionId <subscription-id>;$spn=(Get-AzureRmADServicePrincipal -SPN <Application-Client-Id>);$spnObjectId=$spn.Id;Set-AzureRmKeyVaultAccessPolicy -VaultName <KeyVault-Name> -ObjectId $spnObjectId -PermissionsToSecrets get,list;Once the policy has been set, click the Refresh icon to resolve the permissions error.
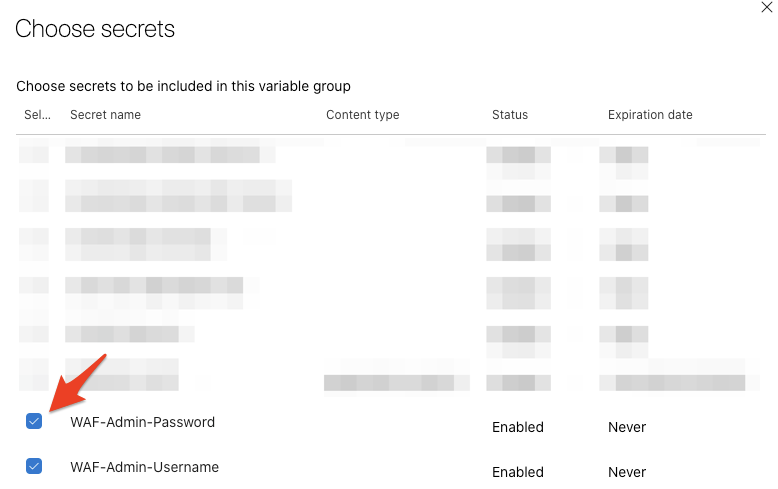
Next step is to link which secrets you wish to include in your Group. Click on Add:

A window will pop-up allowing you to choose which secrets are to be included in the Variable Group:
Finally, to link the Library object (Variable Group) to your pipeline, choose the Link variable group button within the Variable groups section of the Pipeline

This will allow you to choose the Variable Group created in the Library that contains your KeyVault secrets:

You will then notice the appearance of the secrets:

If you follow the practice of having a KeyVault for each environment in Azure, and subsequent stages in Azure Pipelines, the scope for which these apply can be specified:

For more information on adding and using Variable Groups in Pipelines: