Have you ever been responsible for developing and releasing code, but before releasing, you would like to test the code for CVE (Common Vulnerabilities and Exposures)?
There are a number of tools on the market from WhiteSource, SonarQube and Black Duck to name a few. In this article, however, I’d like to talk through implementing Snyk in Azure Pipelines.
What is Snyk?
Snyk is a platform made for developers to automatically detect and fix vulnerabilities associated with Open Source code. Vulnerabilities are checked as you go rather than relying on a single audit, which may not even occur normally.
Where a vulnerability is identified, Snyk will suggest a relevant patch which can be applied and if possible identify and dependencies.
Some refer to analyising code in this manner, where Security is integrated with DevOps, as DevSecOps. I know what you’re thinking, but lets move on…
Snyk in Azure Pipelines
Where you are building code in Azure Pipelines, you can opt to periodically scan your code for vulnerabilities, or each time a commit is made to your repo. Because you can define a task in the pipeline in which to run Snyk, you have control over when and what the scan will assess.
- task: SnykSecurityScan@0
displayName: Snyk Security Scan
inputs:
serviceConnectionEndpoint: 'Azure DevOps - MarkPattonCloud'
testType: 'app'
targetFile: 'src/markpattoncloud.sln'
monitorOnBuild: true
failOnIssues: false
organization: 'mark-patton'Vulnerabilities: An example identified
Having run the above task in my DevOps Pipeline, the completed assessment contains the results. In the completed Release, you can view a summary of the Snyk Report, showing the identified vulnerabilities, rated as High Severity, Medium Severity, etc.

Here is an example of a known vulnerability in my test code. The summary shows the type of vulnerability that has been identified and where in the code it has been introduced:

The Detailed Paths section will show all instances, in the code, where this vulnerability has been found:

The Report goes on to explain some detail about the vulnerability and why it has been flagged as such.

Most importantly, though, it identified the appropriate fix which ought to be put in place by way of Remediation with links to various documents for further Reference:

Setting-Up Snyk
- First, you will need to create an account at Snyk.io.
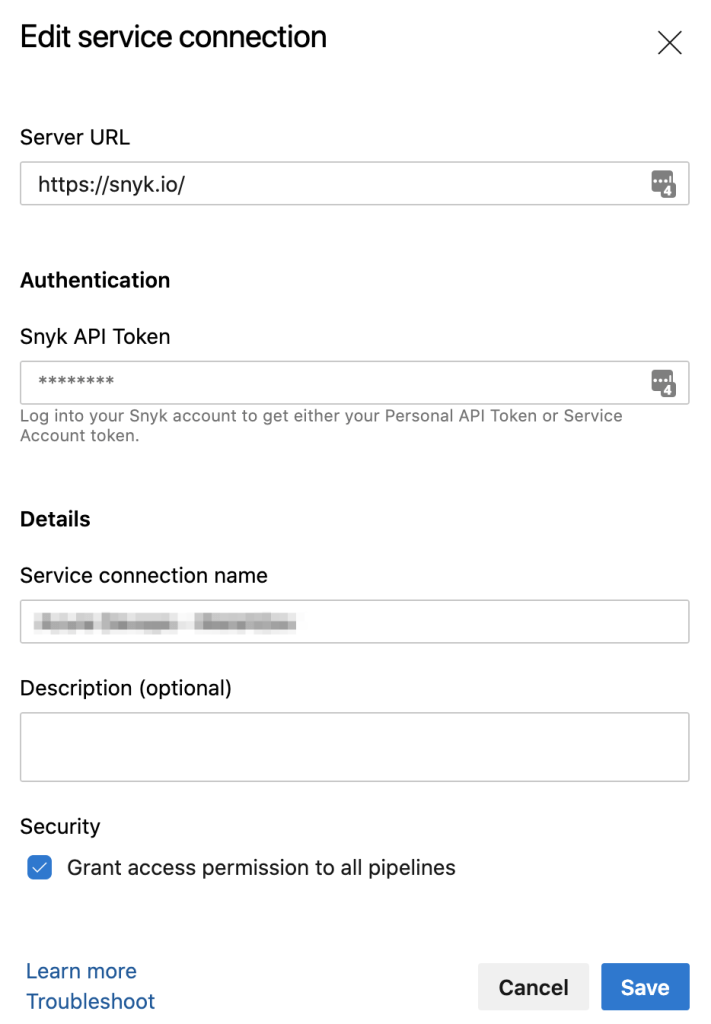
- You will need an API Key, from Snyk, with which to create a Service Connection in your Azure DevOps project. This will connect you to the Snyk service. You can manage your API keys by navigating to General Settings, via the Profile drop-down menu at the top of the Snyk website:
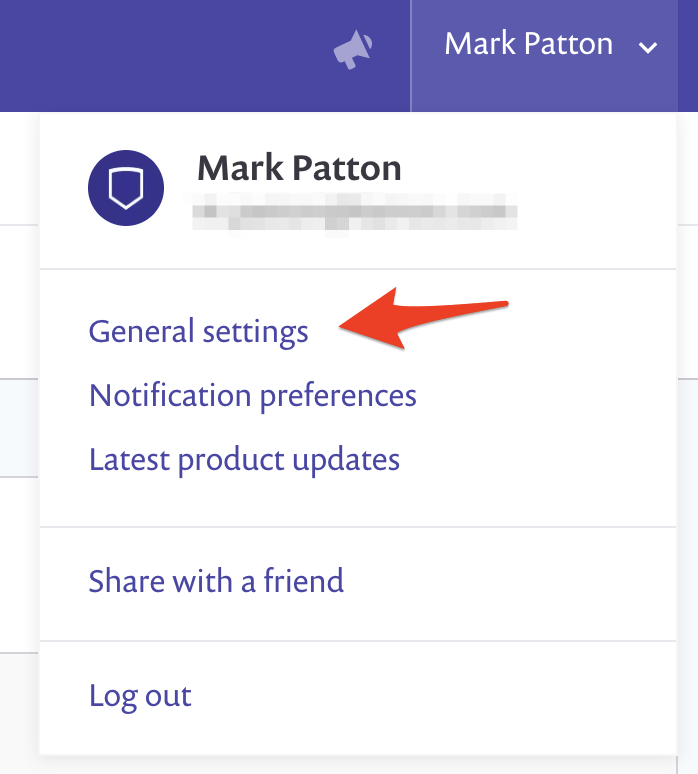
This will show the API Key Management options at the top:

Obtain the API Key by clicking on the box, showing Click to show.
3. Add Snyk, to Azure Pipelines, from the Marketplace

4. Next, create a Service Connection in your Azure DevOps project using the API Key revealed from Snyk.io: